The LabyREnth capture the flag challenge is only open for four more days, but you still have a chance to participate. To help you get started, or move on to the next challenge, our threat research team put together a number of (sometimes cryptic) hints. Whether you’ve been stuck on a challenge and want to move on to the next one, or want to jump in during the final stretch, look no further:
Windows 1:
Watch out for those debugging checks, these XORs aren’t too hard…
Windows 4:
Try harder, with a vengeance! … Or a napkin! … Or a brute forcer!
Unix 1:
How many levels deep does it go?!?! I’d say script it, or maybe bash one liner if you’re extra cool…
Unix 2:
The Program only does one thing, HTTP request and print. Figure out how that HTTP request works…
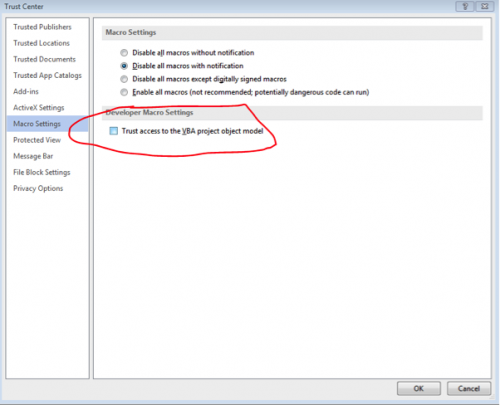
Docs 1:
Use the URL for hints on how to decode part of the URL this naughty macro attempts to download from. Could be base64 and XOR 😉
Docs 4:
Mobile 1:
That seems like a lot of bytes for a call…what do you think RDX?
Mobile 3:
Decompile -> Find -> Replace -> Profit
Threat 1:
sed -e 's/\&L4bry1nth_.*\?//g'
Threat 2:
AAAAAAAAAAA!!!! Compression AAAAAAAAAAA!!!!
Random 1:
Give that environment variable a drink!
Random 3:
Step 1: SYN packet sequence numbers; Step 2: Embedded ZIP; Step 3: Profit!