Don’t miss the breakout and theater sessions, demos, CTF games, parties, prizes and more. Come to Las Vegas — as we showcase the industry’s most comprehensive cloud-native application protection platform (CNAPP) at Black Hat, BSides and Defcon.
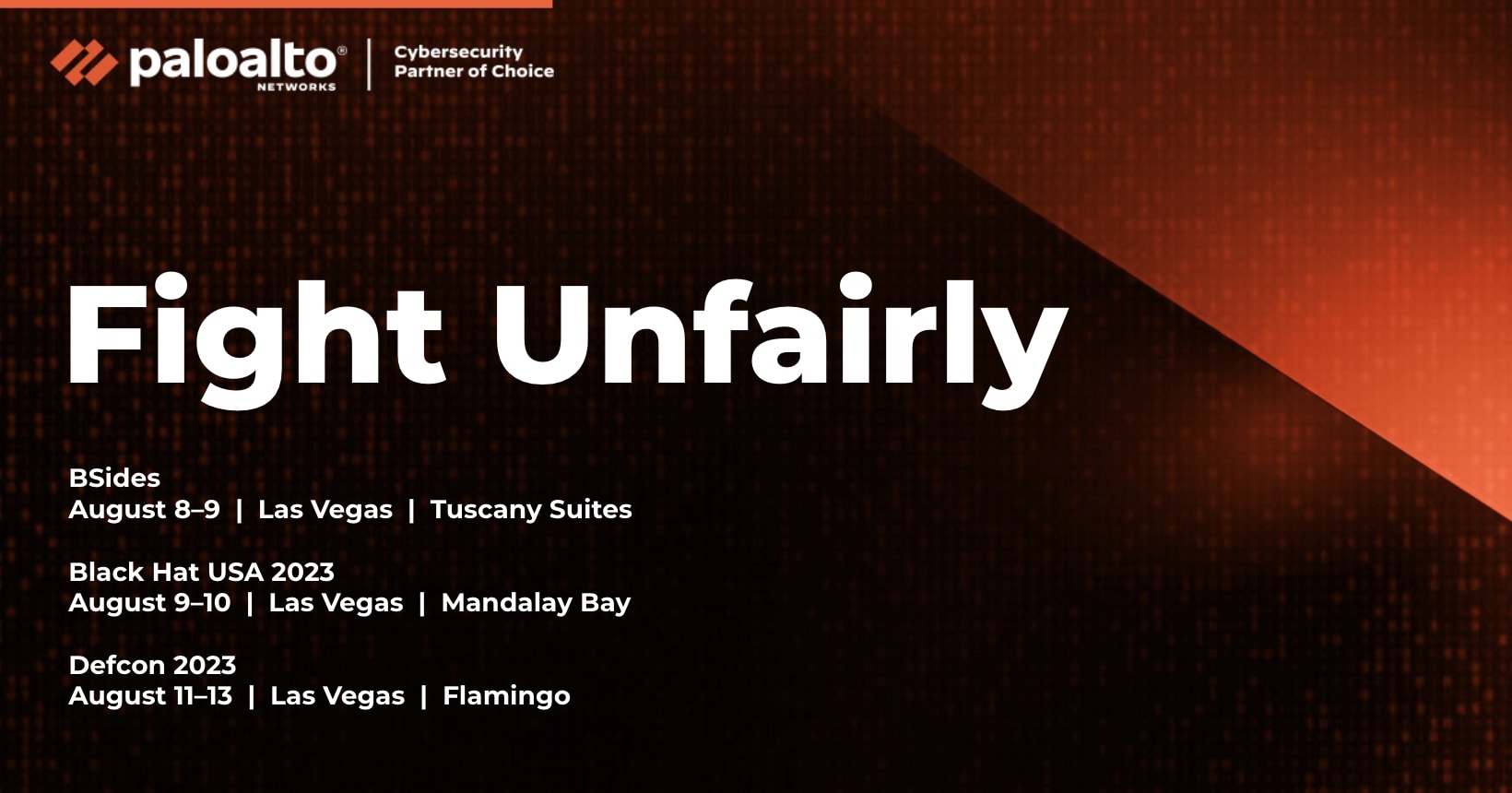
Prisma Cloud is sponsoring three events during the week of August 7 in Las Vegas, Nevada:
-
- BSidesLV, August 8-9
- Black Hat, August 9-10
- Defcon, August 11-13
Secure from Code to Cloud
Prisma Cloud secures applications from code to cloud across multicloud environments. The platform delivers comprehensive security with both continuous visibility and proactive threat prevention throughout the application lifecycle. Prisma Cloud enables security and DevOps teams to effectively collaborate to accelerate secure cloud-native application development and deployment.
BSides Las Vegas: August 8-9
Kick the week off at BSidesLV. Prisma Cloud by Palo Alto Networks is a Gold Sponsor. Stop by the Tuscany Suites and Casino Hotel to chat with our experts and enter our raffle for a chance to win a pair of customized Nike By You shoes.
Speaking Sessions
The GitHub Actions Worm: Compromising GitHub Repositories Through the Actions Dependency Tree
Tuesday, August 8 at 4:00 PM
Presenter: Asi Greenholts, Security Researcher, Palo Alto Networks
How wide can a GitHub Actions worm spread?
In this talk, I’ll demonstrate how a worm can crawl through actions and projects, infecting them with malware.
We will explore the ways in which actions are loosely and implicitly dependent on other actions and create a graph-based dependency tree for GitHub actions. This map will set the path for the worm searching its way to infecting as many action dependencies and GitHub projects as possible.
Join this talk to learn about the methods our worm uses to make its way toward other actions, to get familiar with the high profile open-source projects we could hijack, and to see this worm demoed in action.
Actions Have Consequences: The Overlooked Security Risks in Third-Party GitHub Actions
Wednesday, August 9 at 2:30 PM
Presenter: Yaron Avital, Security Researcher, Palo Alto Networks
After reviewing the build logs of public CI pipelines, I noticed security issues related to permissions and build integrity. To investigate the extent of the problem, I analyzed the build logs of the top 2,000 starred repositories on GitHub, and the results surprised even me.
In this talk, I’ll share my findings on how the world's most popular repositories fail to manage their build permissions — and how these failures can lead to severe consequences, such as creating tokens to access cloud resources or introducing malware to repository code and artifacts.
Next, I’ll uncover the existence of "unpinnable actions." We’ll challenge a highly recommended countermeasure for protecting against compromised third-party actions — pinning. Pinning supposedly assures that the action's code can’t be tampered with, but new malicious code can still sneak into your pipeline, even when pinned. I’lll share conditions that make an action unpinnable and reveal how the world's most popular actions we all use and pin are actually unpinnable.
Black Hat USA: August 9-10
Palo Alto Networks is a Platinum Sponsor of Black Hat 2023 and is delivering live speaker sessions, as well as in-booth theater presentations with demos and after-hours fun.
Visit Booth #1332 at the Mandalay Bay convention center in Las Vegas to chat with Prisma Cloud experts. Attend in-booth presentations and breakout sessions and experience personalized demos of Prisma Cloud. When you get your badge scanned at both booths, you’re automatically entered into our daily raffle to win a pair of Apple Airpods Max!
Join Prisma Cloud for coffee on Wednesday, August 9 from 10:00 a.m. to 2:00 p.m. in the Palo Alto Networks booth (#1332). Open to attendees.
Related: Black Hat Executive Q&A with Wendi Whitmore, Senior Vice President, Unit 42, Palo Alto Networks
Speaking Sessions
What You Don’t Know CAN Hurt You: Unit 42 Global Attack Surface Findings
Thursday, August 10 from 11:30 AM - 12:20 PM
Presented by: Josh Costa, Director, Product Marketing, Palo Alto Networks
If you don’t know about a problem, you don’t have to worry about it, right? Well, not when it comes to your unknown internet-accessible attack surface. We've discovered that attackers initiate attacks within hours of a CVE publication. It’s important that you find and fix those security risks before they become an incident. Join this session to hear about the most common attack surface exposures we’ve found on the global attack surface of large enterprises and national governments. You’ll also learn best practices for managing your dynamic attack surface and how to fight back.
When a Zero-Day and Access Keys Collide in the Cloud: Responding to the SugarCRM 0-Day Vulnerability
Thursday, August 10 from 2:30 - 3:00 PM
Presented by: Margaret Zimmermann, Consultant, Palo Alto Networks Unit 42
How could a zero-day web vulnerability lead to a near complete compromise within an AWS environment? Pretty easily actually.
While the SugarCRM CVE-2023-22952 0-day authentication bypass and remote code execution vulnerability might seem like a typical zero day, the infrastructure behind the scenes of the web application causes the most concern and potential for mayhem if not secured correctly. When a threat actor shows signs of AWS knowledge, the sky's the limit for what they can accomplish with the right permissions.
This presentation maps out various attacks against AWS environments following the MITRE ATTACK Matrix framework, and wraps up with the multiple prevention mechanisms an organization can put in place to protect themselves. The complexity of the attacks details how seemingly innocuous AWS API calls lead to more daunting — and not always traceable — activity. One size does not fit all in cloud security, but these attacks highlight key areas to focus on to make sure you're ready to defend against those attacks when they come.
Prisma Cloud In-Booth Presentations:
- Keys to Effective Web Application and API Security by Ben Nicholson on 8/9 at 10:15 AM
- Finding Sarah Connor - Supply Chain Weakest Links by Stephen Giguere on 8/9 at 2:45 PM
- Real DevSecOps - Easy Developer Centric Security by Stephen Giguere on 8/10 at 11:15 PM
- Build Better Roads Before Better Cars by Stephen Giguere on 8/10 at 2:45 PM
Executive Meeting Requests: Visit with Prisma Cloud at Black Hat
Customer and partner engagement is important to us because it’s the building block of your experience and our relationship. If you’d like to schedule a meeting with Prisma Cloud subject matter experts, executives or sales reps, we’ll be available.
Join Us for a Sushi and Spirits SOCial on August 9 at Black Hat 2023
Please join Palo Alto Networks on August 9 for a night of excitement and networking at KUMI Japanese Restaurant + Bar, right in Mandalay Bay. The sushi, spirits and music start flowing when doors open at 5:00 p.m. This is an exclusive event, so I urge you to register now to get on the list.
DEF CON 31: August 11-13
Wrap the week up at DEFCON 2023 where Prisma Cloud by Palo Alto Networks is sponsoring the Capture the Flag activity. Participate in an interactive workshop for a chance to win multiple prizes! Our team of experts will be onsite to guide you along the way.
The GitHub Actions Worm: Compromising GitHub Repositories Through the Actions Dependency Tree
Saturday, August 12 at 1:30 PM
Presented by: Asi Greenholts, Security Researcher, Palo Alto Networks
GitHub is the most popular platform to host open-source projects. Not surprisingly, the popularity of their CI/CD platform, GitHub Actions, is rising, making it an attractive target for attackers.
In this talk I’ll show you, using a demo of POC worm, how an attacker can take advantage of the Custom GitHub actions ecosystem by infecting one action to spread malicious code to other actions and projects.
We’ll start by exploring the ways in which actions are loosely and implicitly dependent on other actions. This will allow us to create a dependency tree of actions that starts from a project we want to attack and hopefully ends in a vulnerable action we can take control of.
We’ll then dive into how GitHub Actions is working under the hood. I’ll show you how an attacker in control of an action can utilize the mechanism of the GitHub Actions Runner to infect other actions dependent on their action and eventually infect the targeted project.
Finally, after we’ve gained all the theoretical knowledge, I’ll show you a demo with POC malware spreading through actions, and we’ll talk on how to defend against this kind of attack.