SOAR vs. SIEM: What Is the Difference?
SOAR (security orchestration, automation, and response) and SIEM (security information and event management) are indispensable cybersecurity tools catering to distinct functions.
SOAR automates and coordinates security incident response, reducing the workload on security teams. It is beneficial for handling repetitive tasks, allowing analysts to focus on complex threats.
On the other hand, SIEM combines security information management (SIM) and security event management (SEM) into one system. It collects and analyzes security data from multiple sources to detect and respond to security events in real-time.
While SIEM primarily focuses on collecting and analyzing security event data, SOAR extends these capabilities through automation, orchestration, and predefined incident response playbooks.
The Next-Gen Cyber Security Platform You Need | Cortex XSIAM
The Differences Between SIEM and SOAR
SOAR and SIEM exhibit significant differences in their functions and capabilities. These differences are instrumental in understanding how each tool contributes to a comprehensive security strategy:
- Focus and Purpose:
- SOAR platforms primarily focus on automating and orchestrating incident response processes, allowing security teams to respond quickly and efficiently to security incidents and threats.
- SIEM systems are designed to collect, correlate, and analyze security event data from various sources to provide insights into potential security issues but offer a different level of automation for incident response.
- Automation:
- SOAR solutions offer extensive automation capabilities, enabling the execution of predefined actions and workflows in response to security events or incidents. This automation reduces manual intervention and response time.
- SIEM systems provide a different level of automation for incident response. They focus more on data aggregation, correlation, and reporting.
- Integration:
- SOAR platforms are known for their ability to integrate with a wide range of security tools and technologies, allowing for seamless communication and orchestration between different security solutions.
- SIEM solutions typically integrate with various data sources to collect and centralize security event data but may offer a different level of integration for automated incident response actions.
- Incident Response:
- SOAR platforms excel in incident response by providing a war room for incident investigation and collaboration, automating repetitive tasks, orchestrating incident workflows, and enabling security teams to respond rapidly to incidents, reducing mean time to resolution (MTTR).
- SIEM systems provide visibility into security events and can generate alerts. Still, they rely on human analysts to investigate, assess, and respond to incidents, which can lead to longer response times.
- Scalability:
- SOAR solutions are scalable and adaptable to various security environments, making them suitable for organizations of different sizes.
- SIEM solutions can be resource-intensive and may require substantial hardware and software infrastructure for larger organizations.
What are the Benefits of SIEM?
SIEM systems offer a multitude of benefits that are essential for organizations aiming to fortify their cybersecurity defenses:
Enhanced Security Monitoring Through Data Collection and Analysis
SIEM tools are instrumental in monitoring network activity and security events in real-time. They collect data from various sources, allowing for the rapid detection of potential security threats. SIEM facilitates quick threat detection and response by providing security professionals with real-time visibility.
Improved Incident Response Times Through Real-Time Alerting
SIEM solutions collect and correlate data from multiple sources, enabling real-time identification and prioritization of security incidents. This real-time alerting mechanism empowers security professionals to take swift action, mitigating potential damage and reducing threat response times.
Compliance Adherence Through Advanced Reporting Capabilities
SIEM systems play a pivotal role in ensuring compliance with regulatory requirements. By aggregating and correlating diverse logs and events, SIEM aids in identifying and prioritizing security incidents, thereby reducing response times and mitigating potential damage.
Operational Efficiency Through Automation and Improved Prioritization
SIEM tools have automation features that streamline tasks such as log aggregation, correlation, and alerting. This operational efficiency empowers security analysts to focus on higher-level security concerns and critical tasks. Timely detection and response to security incidents minimize the impact of breaches, reducing potential downtime and mitigating risks associated with data breaches or system compromises.
Holistic View of Security Posture Through Integration with Other Security Solutions
SIEM solutions are known for integrating seamlessly with various security solutions, including firewalls, intrusion detection systems, and antivirus software. This integration allows organizations to gain a comprehensive view of their security environment. Armed with this holistic view, security teams can better understand trends, identify vulnerabilities, and strengthen overall security strategies.
What are the Benefits of SOAR?
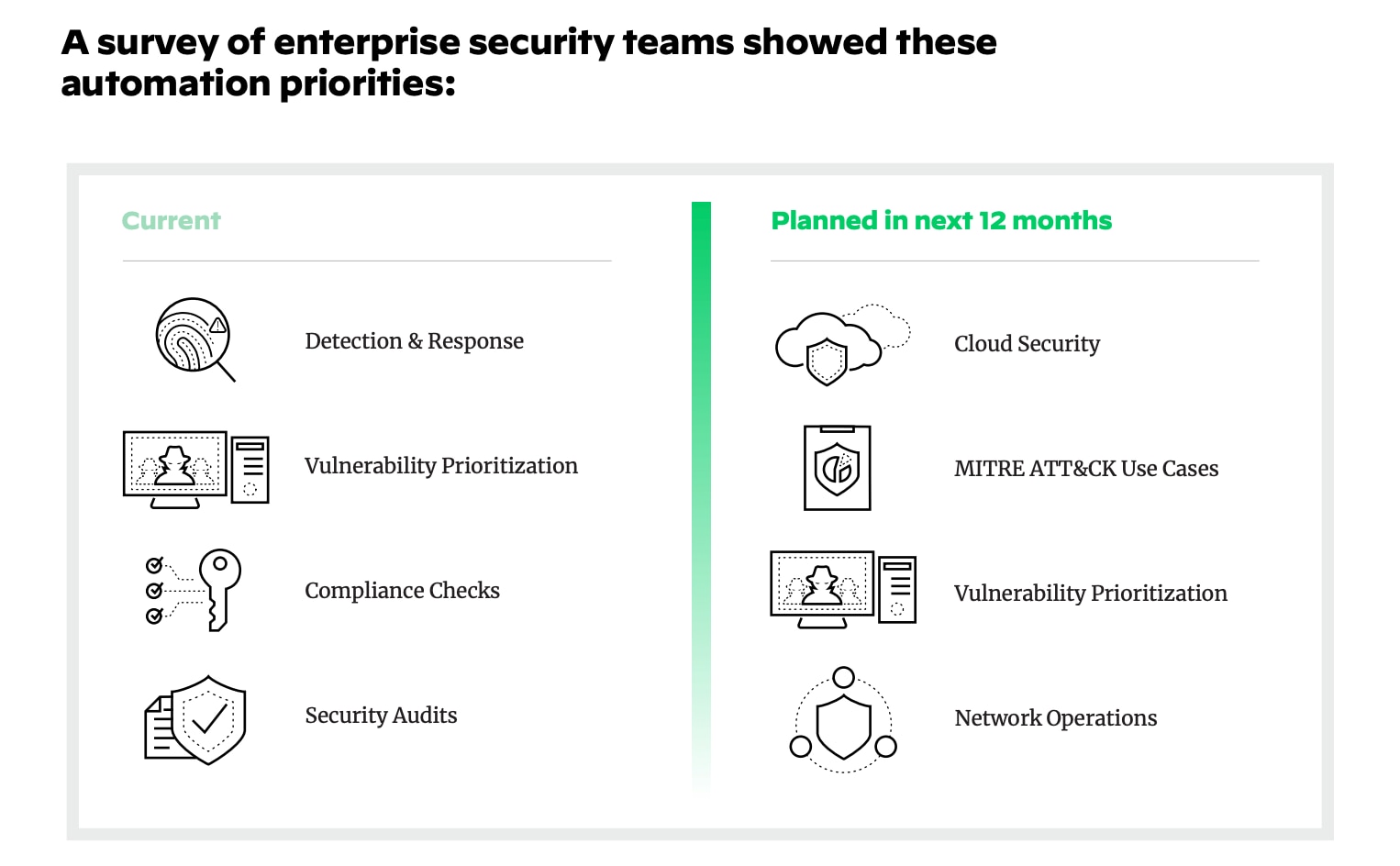
A survey done by Palo Alto Networks of enterprise security teams showed these automation priorities.
SOAR platforms are a cornerstone of efficient and effective security operations. They deliver a wide range of benefits, making them an indispensable asset in the cybersecurity arsenal.
Improved SOC Efficiency by Automating Incident Response
One of the most significant advantages of SOAR is its ability to automate incident response workflows. SOAR frees security analysts to focus on critical incidents by automating repetitive tasks and integrating various security tools. SOAR offers predefined playbooks for different use cases, such as indicator enrichment, alert deduplication, phishing responses, ransomware responses, threat intelligence feed management, malware investigations, and IT operations tasks like employee onboarding and offboarding.
Responds to Incidents with Speed and at Scale
Efficiency is at the core of SOAR's design. It streamlines security processes, connects disparate security tools, and balances machine-powered security automation and human intervention. This approach enables organizations to perform security operations and incident responses efficiently, even at scale.
Ingests, Searches, and Queries All Security Alerts
Complex, real-time investigations occasionally require human intervention. SOAR ensures that analysts can access lightning-quick search, query, and investigation tools to accelerate incident response. By unifying alerts, incidents, and indicators from any source on a single platform, SOAR empowers security teams to respond swiftly and effectively to evolving threats.
Facilitates Analyst Collaboration on Investigations
SOAR promotes collaboration among security analysts with its collaborative investigation features. Analysts can assist each other, run real-time security commands, and learn from each incident through auto-documentation of all actions.
Acts on Threat Intelligence with Agility and Confidence
Unifying, aggregating, scoring, and sharing threat intelligence can be seamless through SOAR's playbook-driven automation. Some SOAR solutions provide built-in, high-fidelity threat intelligence, which can be further enriched by incorporating additional third-party threat intelligence feeds. This approach allows organizations to better identify and prioritize critical threats with agility and confidence.
By understanding the differences and benefits of SOAR and SIEM, cybersecurity professionals, including security analysts, SOC managers, and CISOs, can make informed decisions to strengthen their organization's security posture. The combination of these tools forms a robust cybersecurity strategy that efficiently detects, responds to, and mitigates evolving threats in today's complex threat landscape.
Learn more about Cortex XSOAR.
Learn more about this new approach to security operations by reading, What is Cortex XSIAM?.